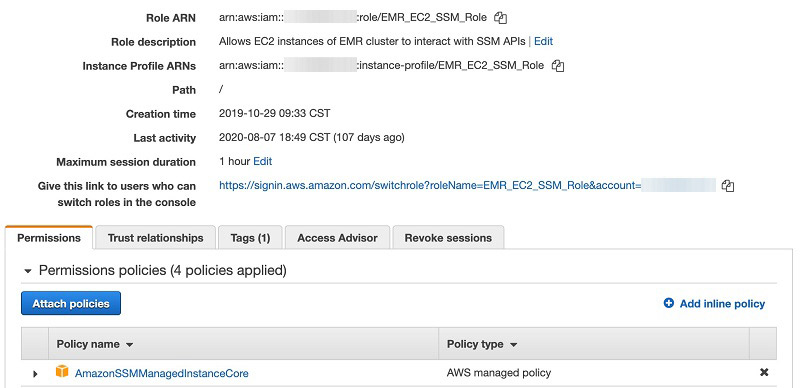
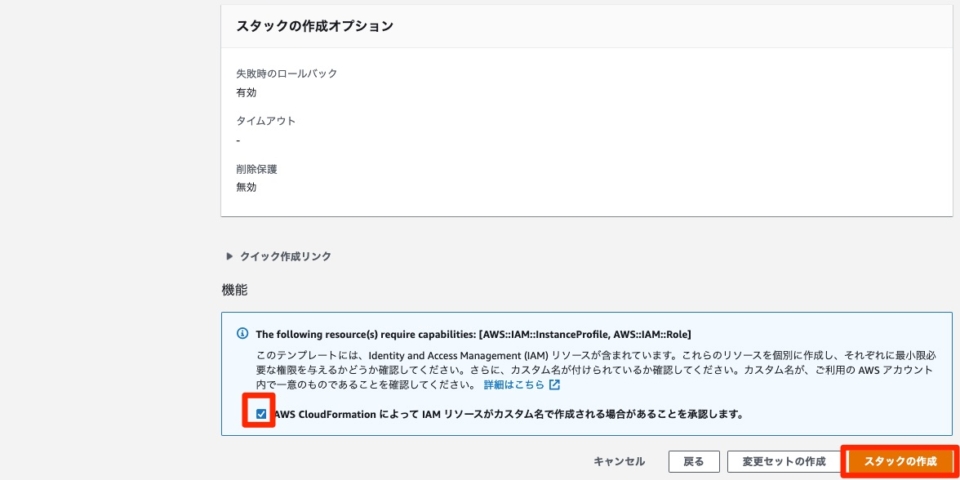
Additionally, both the service role (AWSCloud9SSMAccessRole) and the IAM instance profile (AWSCloud9SSMInstanceProfile) were created automatically for you by the CloudFormation template The managed policies included in the service role are AWSCloud9SSMInstanceProfile and AmazonSSMManagedInstanceCoreI was playing around with Sagemaker notebook and EMR functionality recently I was looking for some r eady made cloudformation examples which bootstrapped a sagemaker notebook which was provisioned with a connection to an EMR cluster This AWS blog looked interesting I was able to grab the cloudformation template, but was not interested in kerberizing the setup as wasThe AWSSSMAssociation resource creates a State Manager association for your managed instances A State Manager association defines the state that
How To Install Ssm Agent On Linux Ec2 Instances
Amazonssmmanagedinstancecore cloudformation
Amazonssmmanagedinstancecore cloudformation-Establishing SSH Tunnel To begin, run the command ssh L 5432`terraform output raw rds_endpoint` Nf ubuntu@`terraform output raw bastion_ip` Breaking this down, it says ssh ubuntu@ terraform output bastion_ip Let's ssh to the bastion server we just created Veni, vidi, vici Run ssh and scp with AWS Session Manager Terrence Miao's Adventures A journey of a thousand miles begins with a single step




How To Secure Your Instance Metadata Service On Aws Using Aws Systems Manager Run Commands Cevo
Running pulumi up and we have output about our EC2 after a few seconds Next, using SSM to connect (check here to set up the CLI), we just run aws ssm startsession target and we are in!What is exciting here is the whole script feels like familiar Typescript As much as I like working with Terraform or CloudFormation, those unfamiliar are sometimes CloudFormation definition Here's the CloudFormation for two additional resources, that sneakily I've already included in the CloudFormation template linked to earlier The MetricFilter CloudFormation resource looks for any occurrence of the phrase 'password changed' and creates a metric called ChangePassword when one is foundThe role in question has only AmazonSSMManagedInstanceCore attached Removing the policy allows the stack to be deleted cleanly Environment **CDK CLI Version Did AmazonSSMManagedInstanceCore get attached by some other mechanism after creating the Role using CloudFormation?
A Role that can assume permissions for SSM tasksInventory Management Tools Systems Manager AWS Systems Manager is a collection of features that enable IT Operations that we will explore throughout this lab There are set up tasks and prerequisites that must be satisfied prior to using Systems Manager to manage your EC2 instances or onpremises systems in hybrid environments You must use a supported operating If you have an off the shelf AMI, just make sure that the AmazonSSMManagedInstanceCore policy is attached to the instance profile for the instance When the instance starts up, you should be able to go to the connection console in EC2 and see this SSM set up successfully Click Connect and move on to the next step
On Ubuntu LTS Create CFn Preparing helper scripts Immediately install the cloudwatch agent using the helper script! After the Part 1 post, which specifically explaining configuration with packer, on this part, I'll write more about Terraform and AWS CodebuildThe CloudFormation templates included in this repository are intended to assist you in configuring and installing Amazon CloudWatch and AWS XRay for on premises servers, Amazon EC2, Amazon ECS, and Amazon EKS Templates are also provided for deploying ECS and EKS clusters and services with Amazon



1



Applying Managed Instance Policy Best Practices Aws Management Governance Blog
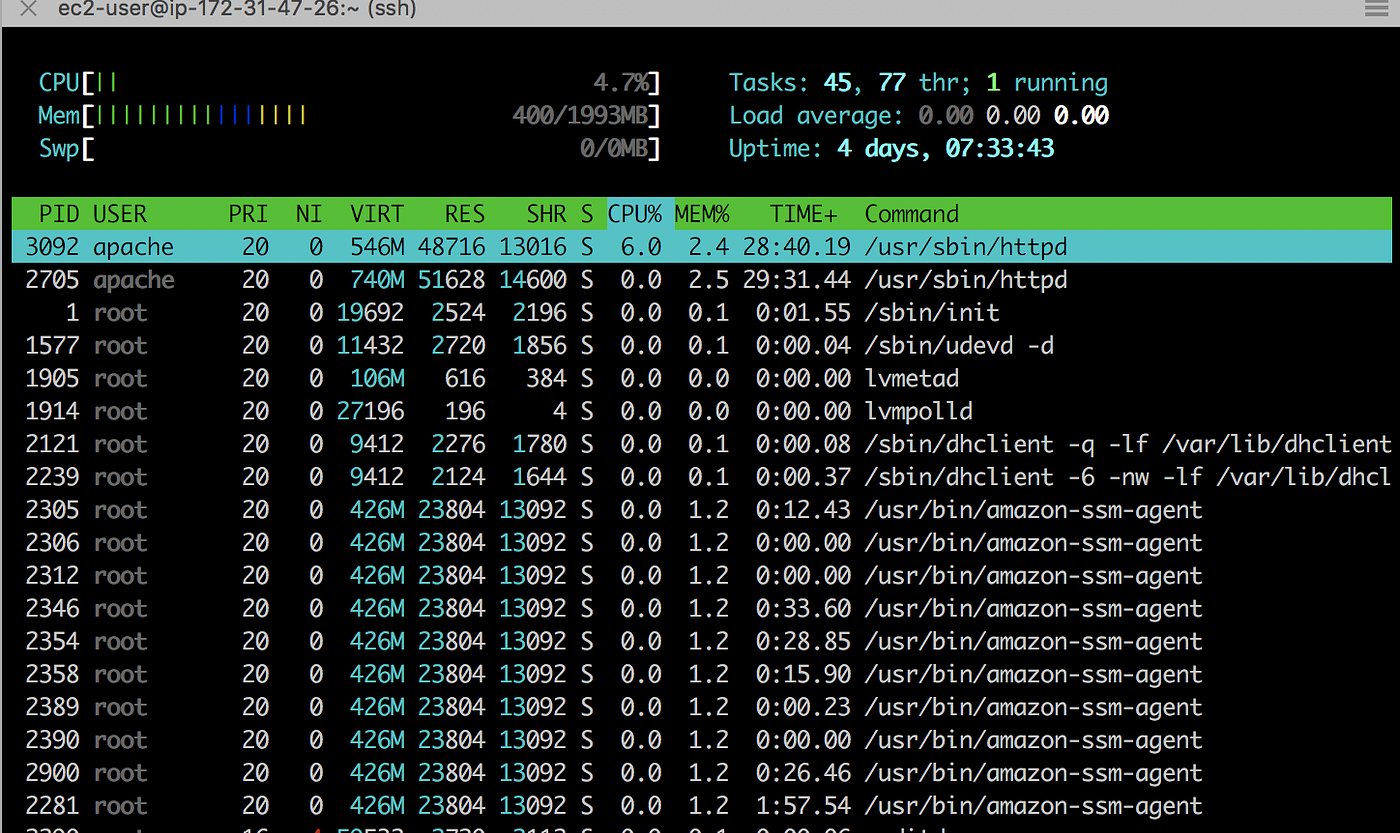
In the final part of this series, I will demonstrate how to configure EC2 Instance Metadata Service (IMDS) through the use of AWS Systems Manager (SSM) Run Commands using a tag based approach to target EC2 instances to run our IMDS commands against In addition, I will look at automating this process using EventBridge to maintain IMDS on a periodic basis CDK Create EC2 instace in private subnet Install Nginx codestackts Using AWS SSM State Manager you can bootstrap instances with specific software at startup, download and update agents on a defined schedule, including SSM Agent, configure network settings, join instances to a Windows domain (Windows Server instances only), patch instances with software updates throughout their lifecycle or run scripts on



Stackery Announces The Availability Of Bastion Modules On The Cloudformation Public Registry



How To Build An Aws Network Firewall Environment By Giuseppe Borgese Medium
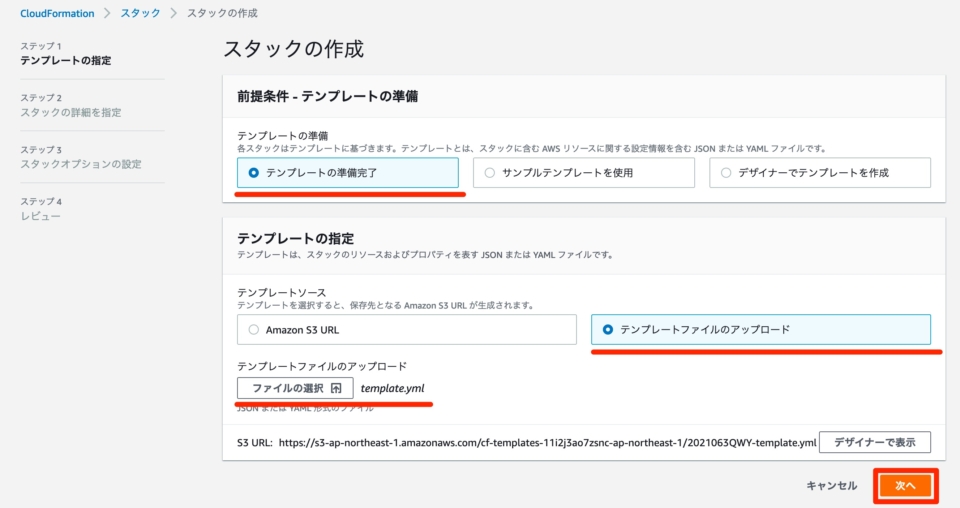
Automated configuration of Session Manager without an internet gateway Session Manager is a fully managed AWS Systems Manager capability that you can use to manage your Amazon Elastic Compute Cloud (Amazon EC2) instances, onpremises instances, and virtual machines (VMs) through an interactive oneclick browserbased shell or through the AWS CLIUnfortunately, it is not installed on Ubuntu by default So, first download the awscfnbootstrap package Add the following script to the helper script in UserDate that is executed when EC2 starts Helper Script Reference Install CloudWatch Open the AWS CloudFormation link in a new tab and log in to your AWS account Click on the stack name, for example cfnworkshopec2 In the top right corner click on Update In Prepare template, choose Replace current template In Template source, choose Upload a template file Click on Choose file button and navigate to your workshop directory




Online Help Forticwp 1 0 Fortinet Documentation Library
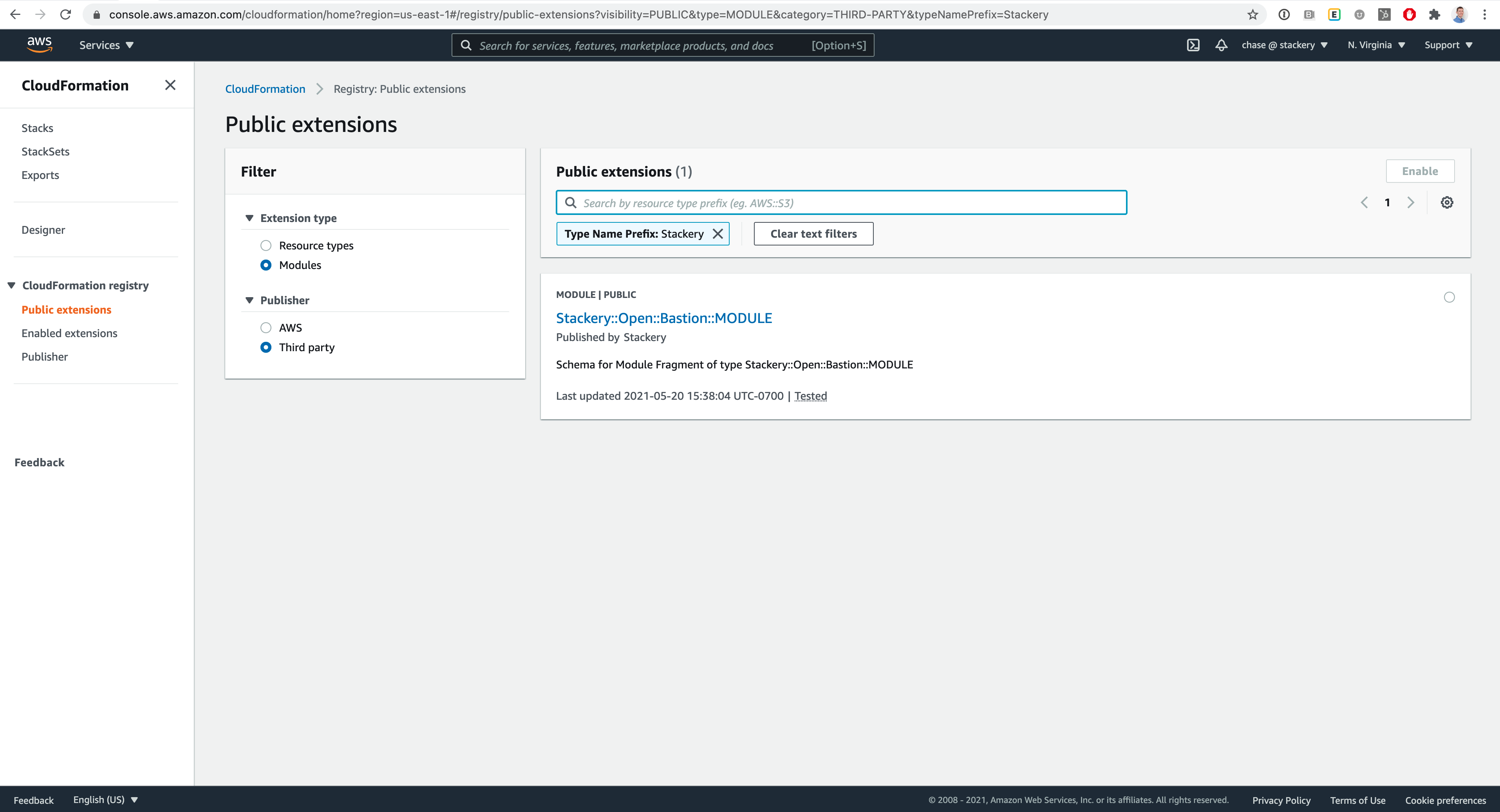



Stackery Announces The Availability Of Bastion Modules On The Cloudformation Public Registry
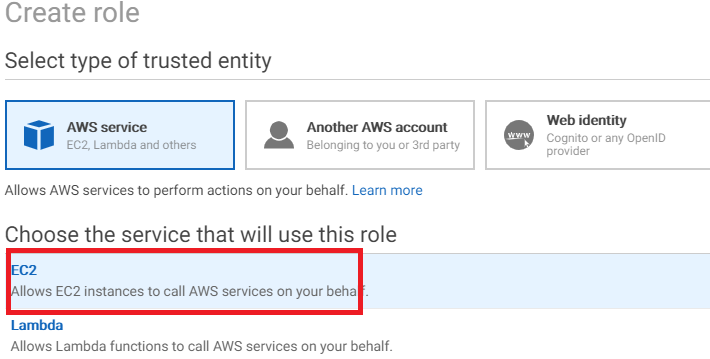
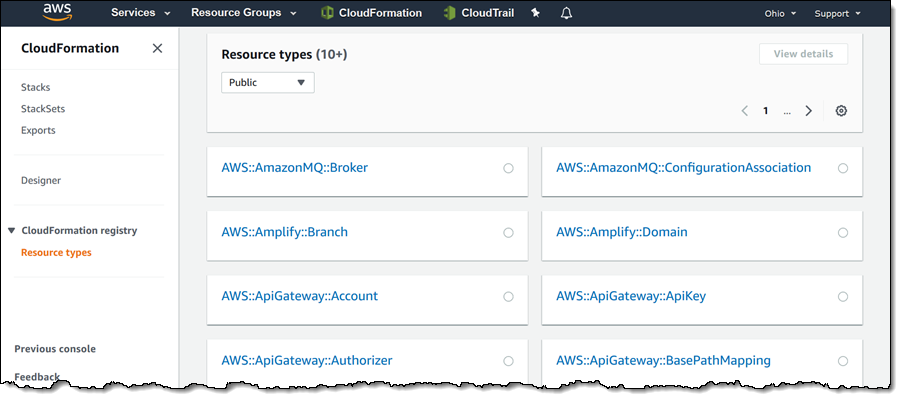
CloudFormation, Terraform, and AWS CLI Templates Configuration to create an IAM role for EC2 instances to access to AWS Systems Manager (SSM) services, with the least permissions required If the user is satisfied with the displayed content, they can click to create a stack Then CloudFormation will start creating resources for you Manually install SSM agent If you want to manually install the SSM agent after creating a role with CloudFormation and attaching it to an EC2 instance, please run the following command in the VM consoleThe full CloudFormation template for deploying a SystemsManager enabled instance with a sample automation document can be found on my GitHub Initial SSM setup In order to leverage SSM, we need a few things An Instance profile we can attach to EC2 instances;




Stackery Announces The Availability Of Bastion Modules On The Cloudformation Public Registry
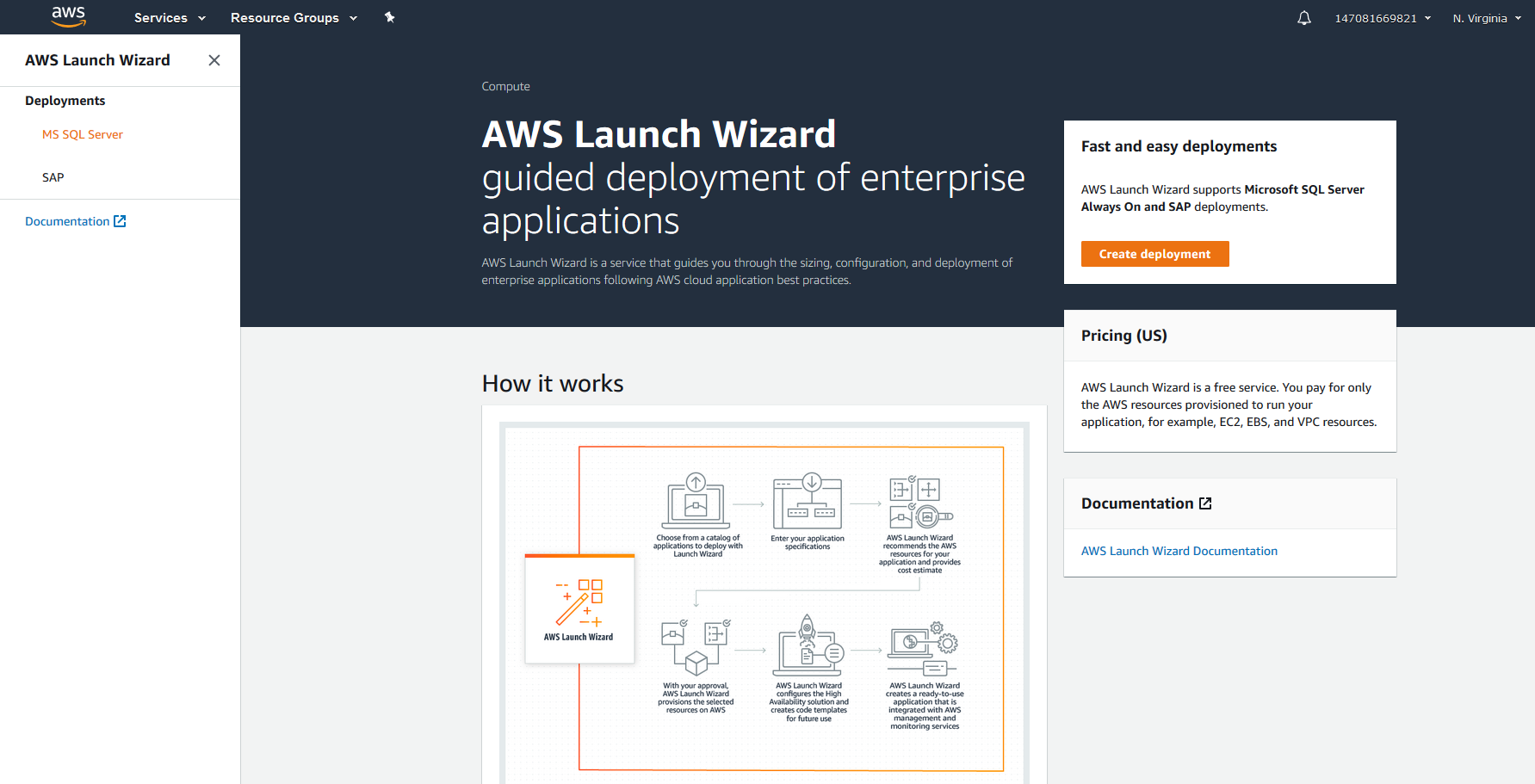



Aws Launch Wizard For Quick Sql Server Always On Deployments
An SSM Role EC2 Instance Profile that will use the role created above The EC2 Instance Security GroupAn IDE to write and edit your CloudFormation Template Step 1 Create EC2 Instance, Profile, and Role Instead of creating the individual resources manually, I used a single CloudFormation template The Template will create; AWS recently enhanced its Systems Manager offering with shell access to EC2 instances and then they enhanced it further with SSH tunnel supportWith these improvements, it's now possible to improve your application's security posture while reducing it's operational costs and simplifying setup/maintenance



Login From Internet Into A Private Subnet With Session Manager By Giuseppe Borgese Medium




How To Achieve A Secure Connection To Ec2 Virtual Servers With Session Manager Without The Need Of Encryption Keys Financial Solutions
By hand using the console, by using some script, by using 1 I am trying to build an ECS cluster via CloudFormation The subnets that the cluster instances will reside in are to be private Additionally, I have created an image from an EC2 I built, and have verified the SSM agent, ECS agent, and cloudinit are installed and running I have also added an inbound rule in my security group to allow HTTPSService Levels Aviator, Manage & Operate Features Rackspace AWS certified engineer response to CloudWatch alarms 24x7x365 Set up CloudWatch alarms to a preconfigured SNS topic or let us do it for you Custom CloudFormation template creation Service Levels Aviator, Architect & Deploy Data restoration support (for EC2 and RDS exclusively



Ecs Role Managed Policy Amazonec2roleforssm Soon To Be Deprecated Issue 109 Aws Samples Ecs Refarch Cloudformation Github




Shipping Aws Ec2 Logs To Cloudwatch With The Cloudwatch Agent Tom Gregory
Lab Setup Setup Managed Instances We will need to have a couple instances deployed to work with throughout the workshop This will be provided to the participants as homework ahead of the day or the workshop to ensure we have enough time to get through the materialIn this tutorial, we will demonstrate how to set up AWS Distro for OpenTelemetry Collector (AWS OTel Collector) on Amazon Elastic Computer Cloud(EC2) to collect application metrics Note This tutorial will set up AWS OTel Collector on an Amazon EC2 instance in _uswest2_ with a provided CloudFormation template if you want to run the example in the other AWS regions, please Amazon Web Services Feed Automated configuration of Session Manager without an internet gateway Session Manager is a fully managed AWS Systems Manager capability that you can use to manage your Amazon Elastic Compute Cloud (Amazon EC2) instances, onpremises instances, and virtual machines (VMs) through an interactive oneclick browserbased shell or
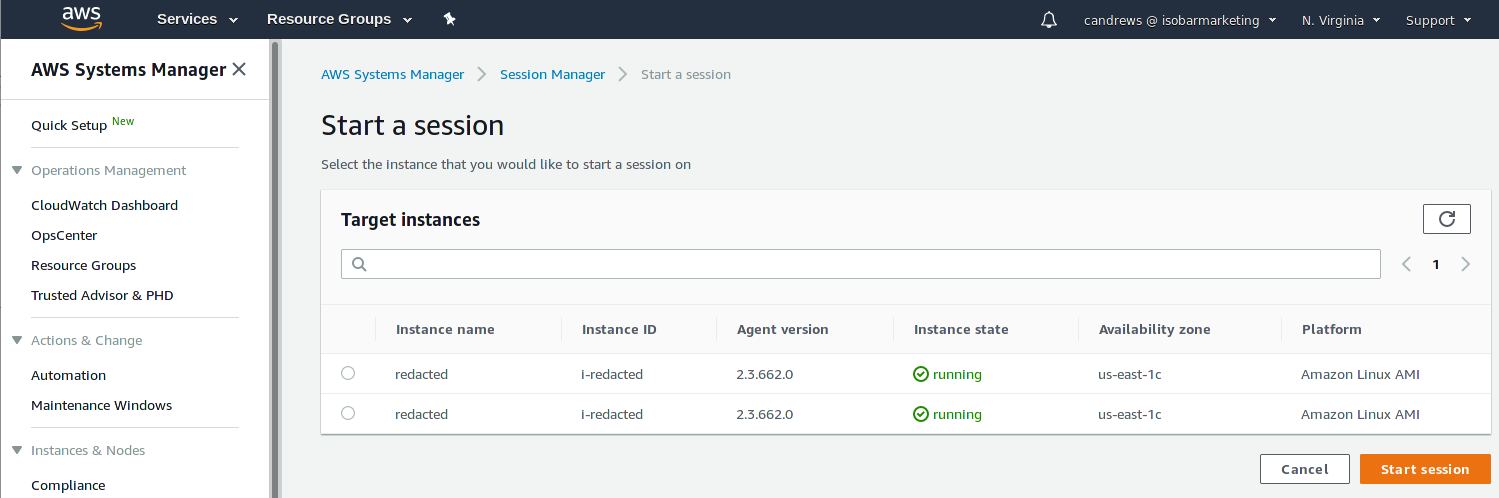



Improve Security And Reduce Costs With Aws Ssm Session Manager Craig Andrews




Preparing Resources On Aws Lamp Platform
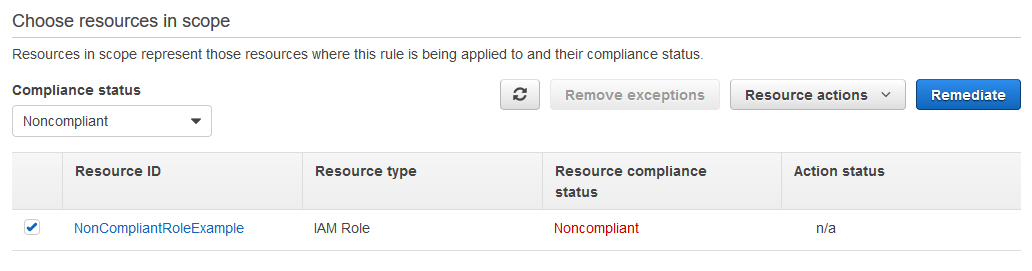
This will read the Cloudformation file and make it available as a high level construct for use with the rest (iamManagedPolicyfrom_aws_managed_policy_name("AmazonSSMManagedInstanceCore"))AWSSSMAssociation The AWSSSMAssociation resource creates a State Manager association for your managed instances A State Manager association defines the state that you want to maintain on your instances For example, an association can specify that antivirus software must be installed and running on your instances, or that certain ports must be closed IAM entities (users, groups, and roles) which are found to have the targeted policy attached are marked noncompliant A custom Systems Manager Automation document allows automated remediation of IAM roles by replacing the targeted policy with a specified list of replacement policies To deploy the




How To Achieve A Secure Connection To Ec2 Virtual Servers With Session Manager Without The Need Of Encryption Keys Financial Solutions



Sai Sriparasa Noise
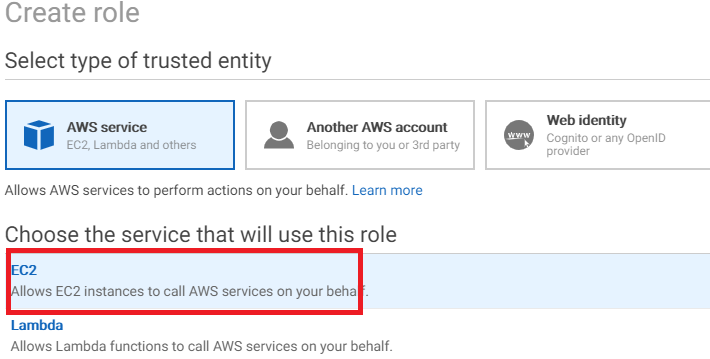
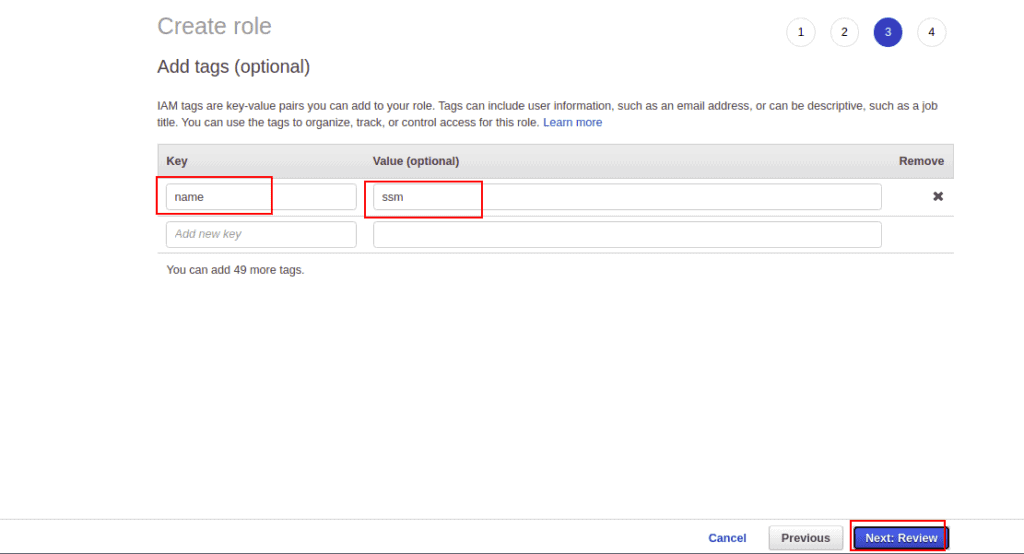
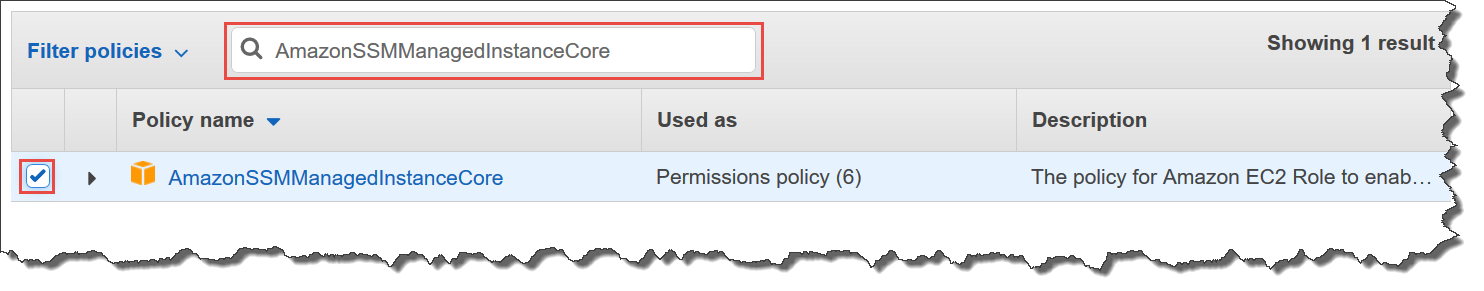
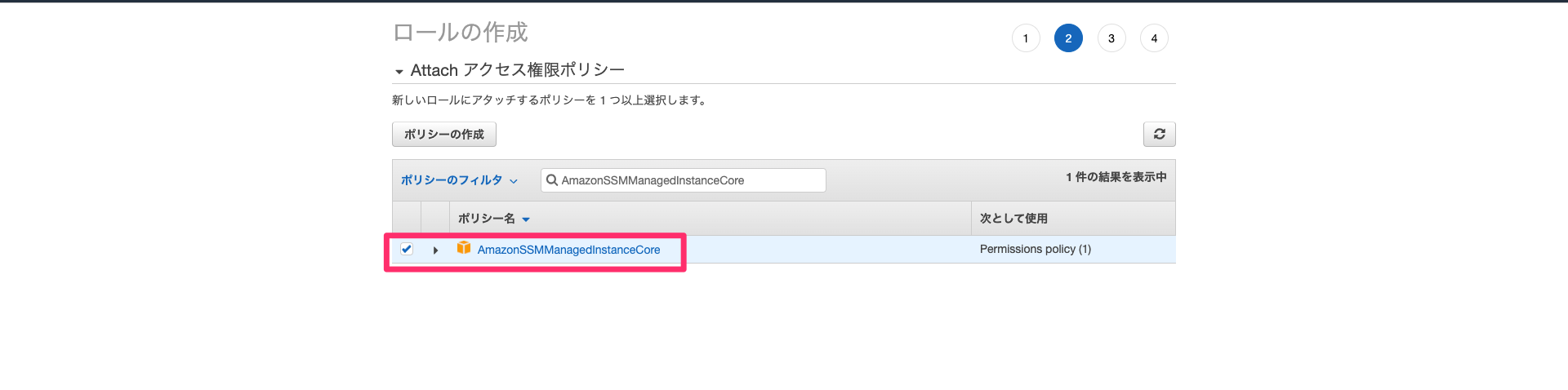
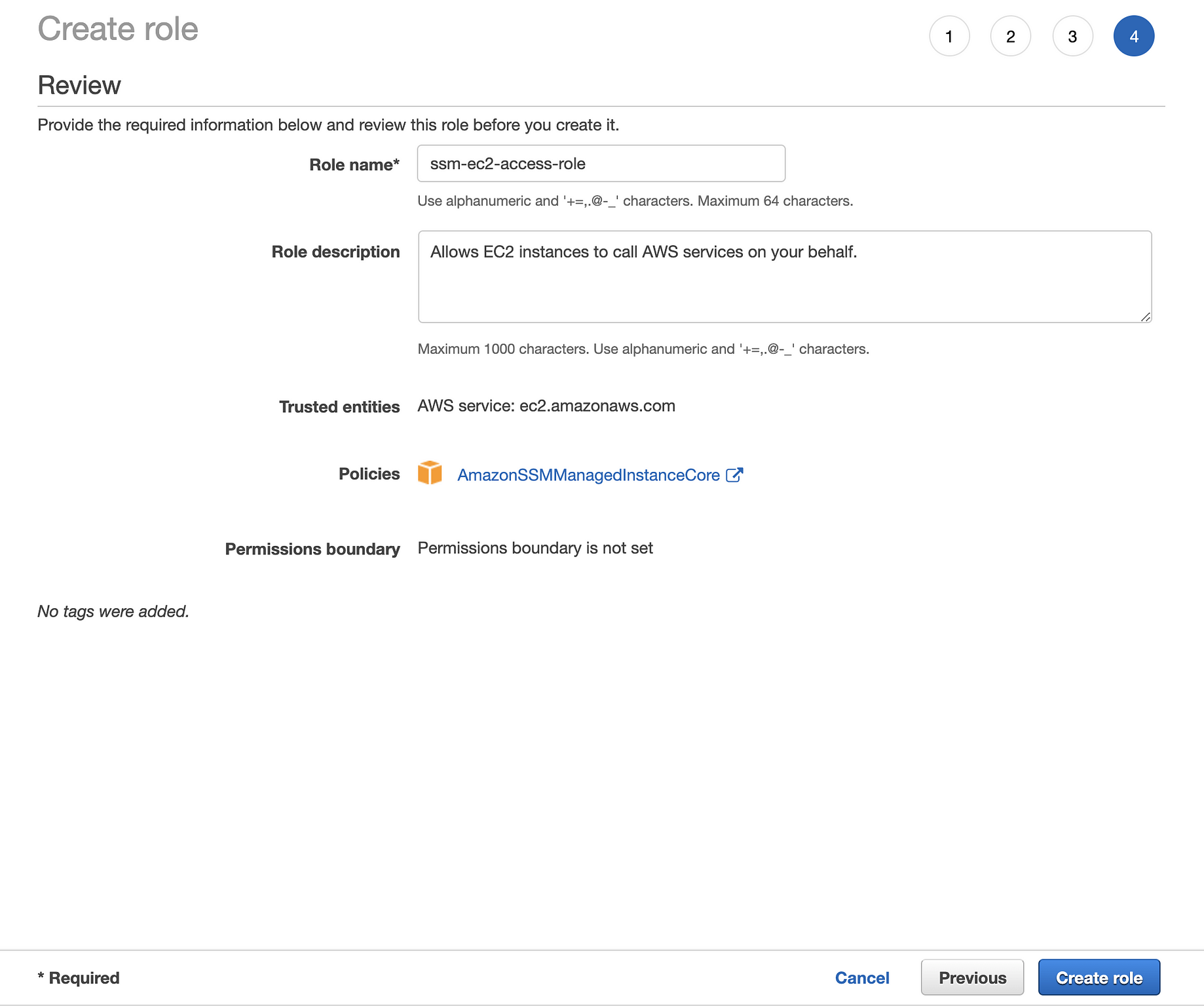
Experiment (CloudFormation) AWS Systems Manager Integration FIS SSM Send Command Setup Linux CPU Stress Experiment Working with SSM documents SSM access to the instance requires an instance role with the AmazonSSMManagedInstanceCore policy attached Serverless, tagbased CloudWatch monitoring of Windows services on AWS EC2 Published on • 6 Likes • 0 CommentsSimply share the CloudFormation with the prooV account number provided to you during the registration process In the Policy search field, search and select AmazonSSMManagedInstanceCore, then click Next s Click Next Review In the Role name field, give any name for the EC2 role




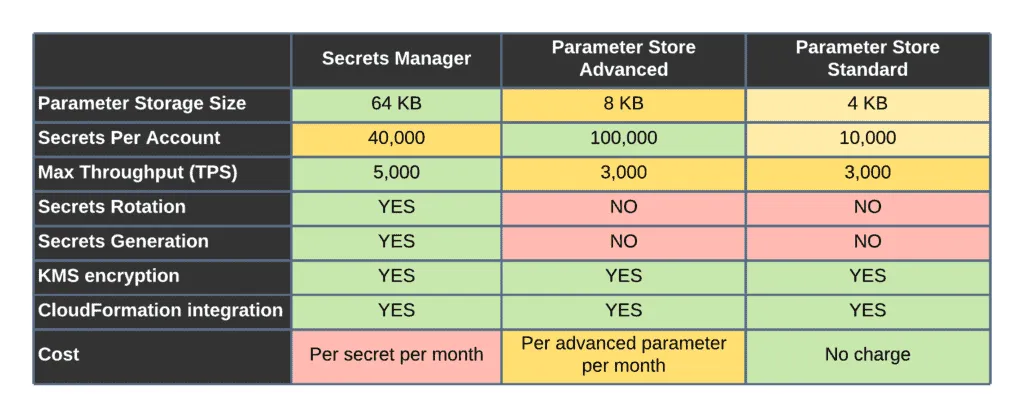
Integrating Aws Cloudformation With Aws Systems Manager Parameter Store Aws Management Governance Blog



How To Install Ssm Agent On Linux Ec2 Instances
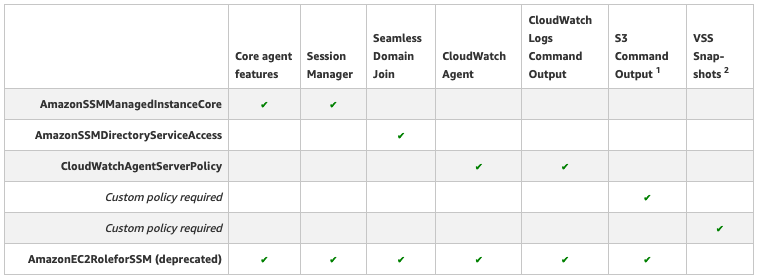
Simply share the CloudFormation with the prooV account number provided to you during the registration process $99/hour as long there are active PoC resources in your account Data Deep Mirroring if selected costs an additional $100/hour This does not include costs stemming from AWS environments and servicesPolicy AmazonSSMManagedInstanceCore Required permissions This AWS managed policy allows an instance to use Systems Manager service core functionality Policy A custom policy for S3 bucket access Required permissions in either of the following casesIn the Policy search field, search and select AmazonSSMManagedInstanceCore, then click Next s Click Next Review In the Role name field, give any name for the EC2 role (Keep the name of EC2 role for use later in attaching the role to the EC2 instance) Click Create role to



Aws Automation




How To Secure Your Instance Metadata Service On Aws Using Aws Systems Manager Run Commands Cevo
The TemplateURL property is used to reference the CloudFormation template that you wish to nest The Parameters property allows you to pass parameters to your nested CloudFormation template 2 Prepare S3 bucket Whilst single templates can be deployed from your local machine, Nested Stacks require that the nested templates are stored in an S3 bucketThis Product Guide provides a detailed look at how Rackspace delivers our Fanatical Support for AWS offering It covers core concepts such as the AWS account structure, Rackspace service levels and advanced concepts such as providing access requests to instances via Rackspace Passport and accessing audit logs via Rackspace Logbook The beauty of CloudFormation shines when we want to delete our resources If we did ClickOps (create resources using the AWS console) then it will be a nightmare to keep track of all the resources and delete them one by one, like doing a treasure hunt With CloudFormation, all we have to do is just delete the stack!




How To Achieve A Secure Connection To Ec2 Virtual Servers With Session Manager Without The Need Of Encryption Keys Financial Solutions




Deploy Ghost On Aws Using Cloudformation Part 03



1
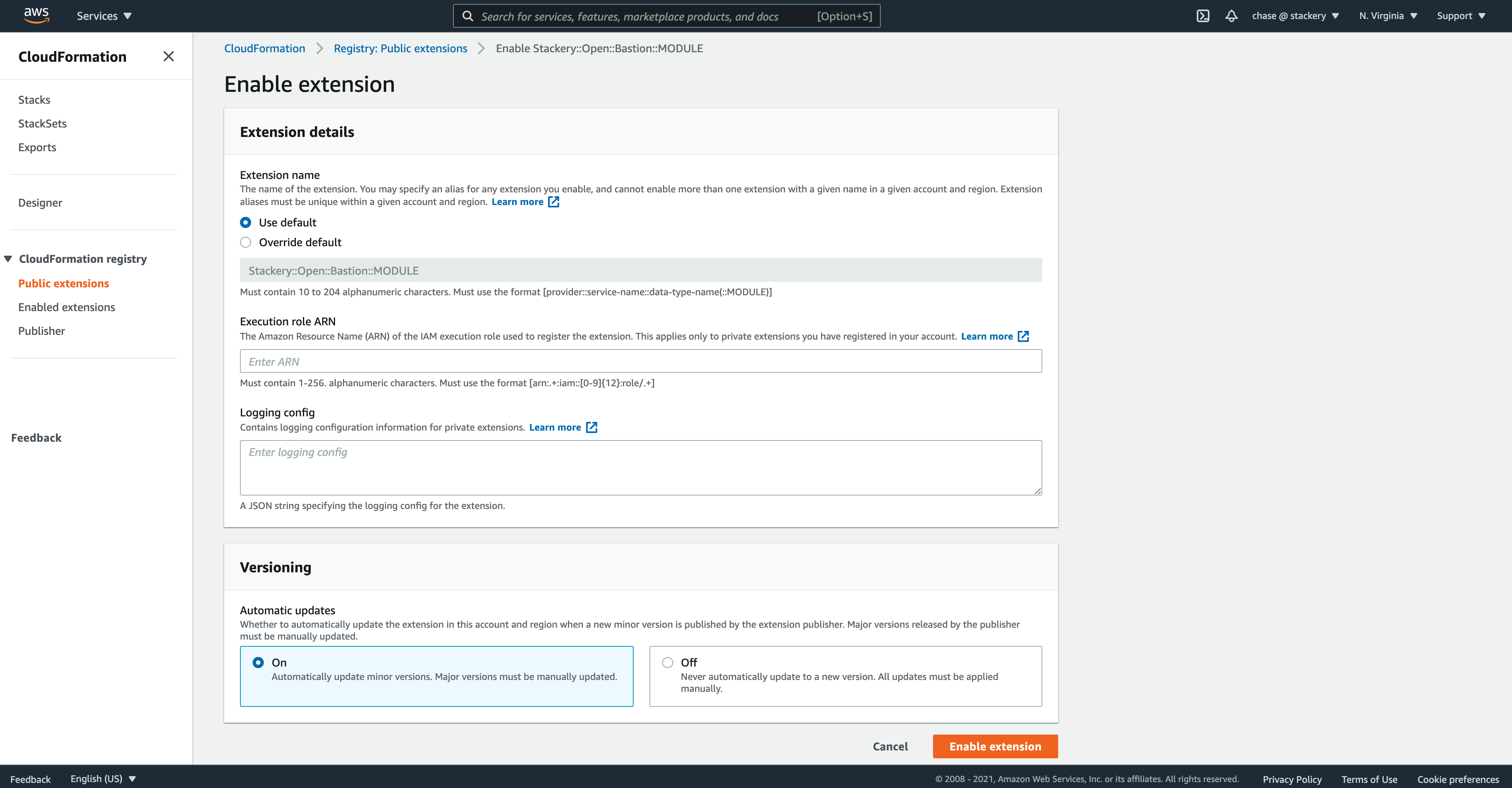



Stackery Announces The Availability Of Bastion Modules On The Cloudformation Public Registry




How To Install Aws Ssm Agent On Centos 8 Centos 7 Computingforgeeks




Introduction To Aws Systems Manager




How To Secure Your Instance Metadata Service On Aws Using Aws Systems Manager Run Commands Cevo



1




Blog Oblivion



News Noise Page 14




Aws 실습 4주차 1 Cloudformation으로 환경배포




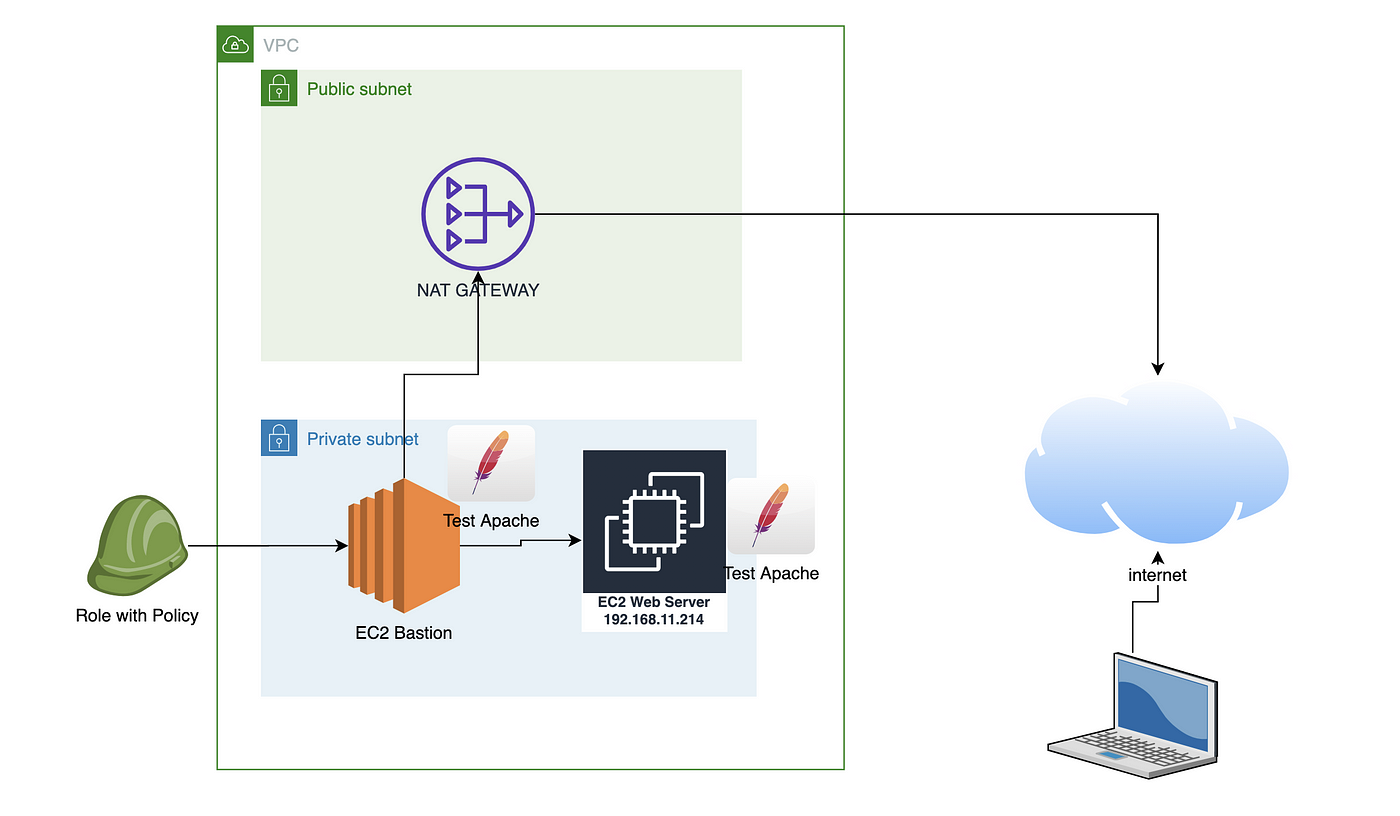
Toward A Bastion Less World Aws



Introduction To Aws Systems Manager



Aws S3 Assets Generated Cloudformation Template Seems To Be Missing Values Issue Aws Aws Cdk Github



Github Aws Samples Aws Config Systems Manager Instance Policy A Solution To Deploy Aws Config Rules To Audit Remediate Iam Entities Which Have Aws Managed Policy Amazonec2roleforssm Attached




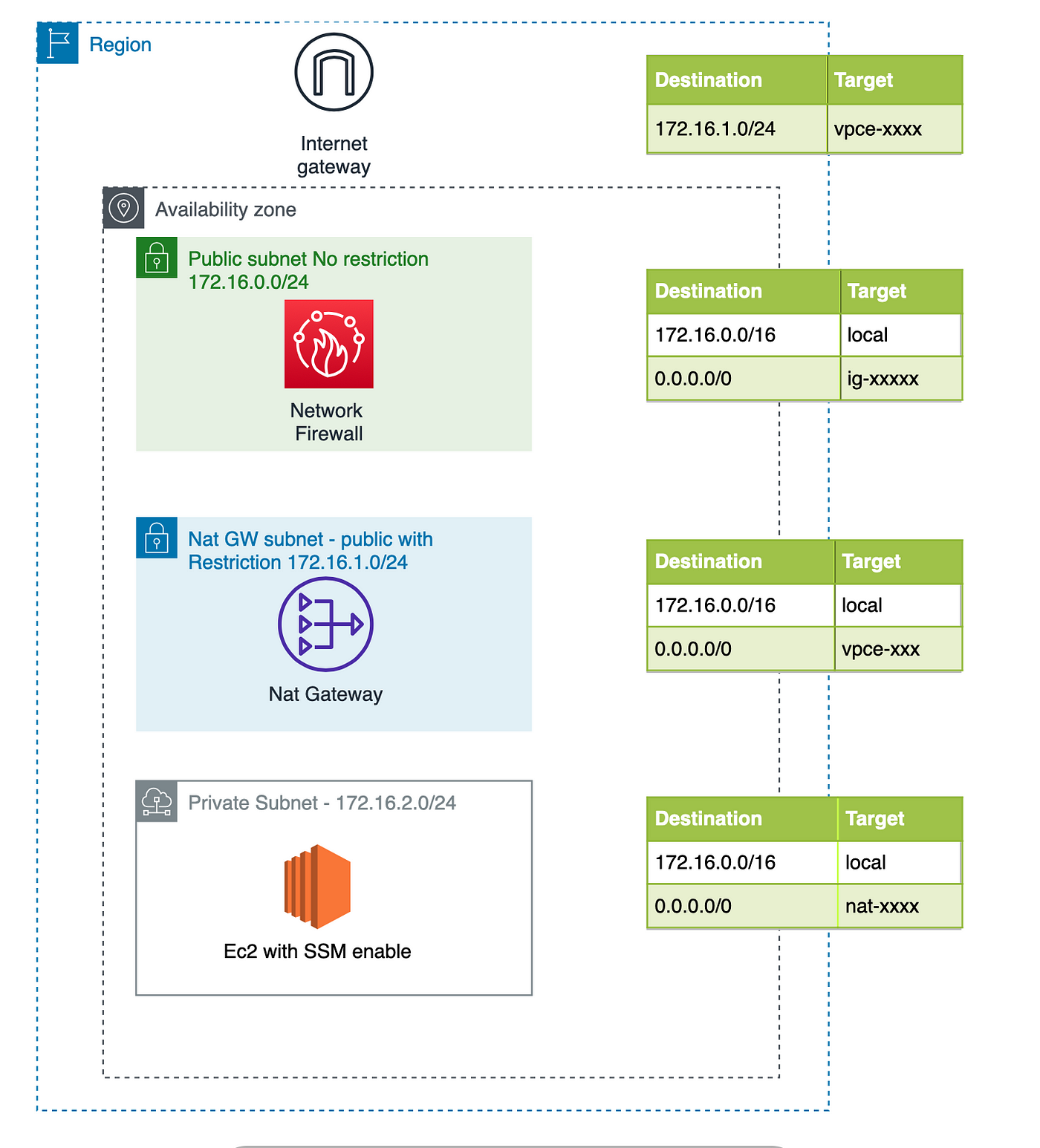
Login From Internet Into A Private Subnet With Session Manager By Giuseppe Borgese Medium




Shipping Aws Ec2 Logs To Cloudwatch With The Cloudwatch Agent Tom Gregory



Step 4 Create An Iam Instance Profile For Systems Manager Aws Systems Manager




Aws Directory Service Noise




How To Secure Your Instance Metadata Service On Aws Using Aws Systems Manager Run Commands Cevo



Sql Server Fciをfsx For Windowsを使って構築する Awsリソース編 Developersio




Integrating Aws Cloudformation With Aws Systems Manager Parameter Store Aws Management Governance Blog
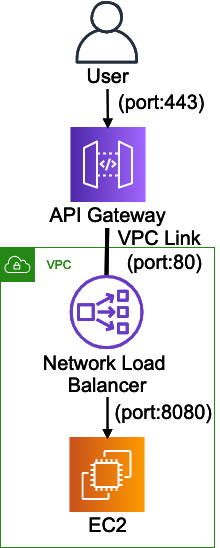



Cloudformationを使ってapi Gatewayとec2でrest Apiを構築してみる Developersio



Aws Systems Managerのパッチマネージャーを使ってパッチ適用を自動化する Qiita




News Noise Page 14



Aws Cloudformation Evaluation Using The Proov Platform
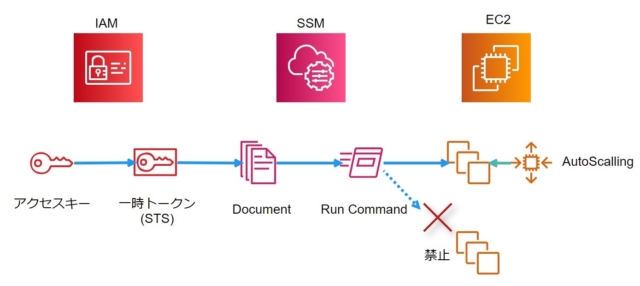



オートスケール起動のec2のリモート操作 Run Command を 権限限定したiamロールで行ってみた Developersio
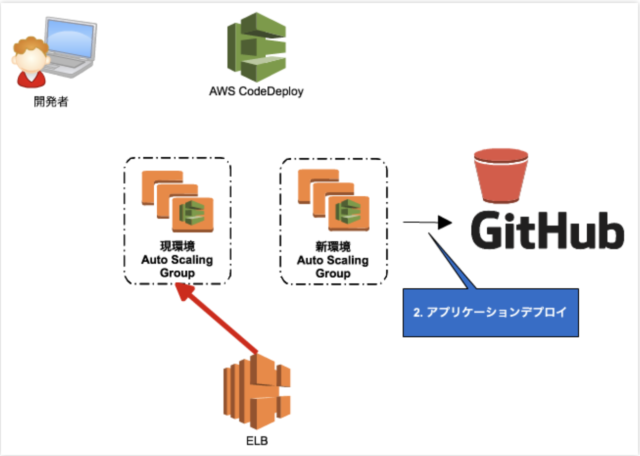



Cloudformation 一撃で Ec2 の Blue Green Deployment の Codepipeline を構築する Developersio
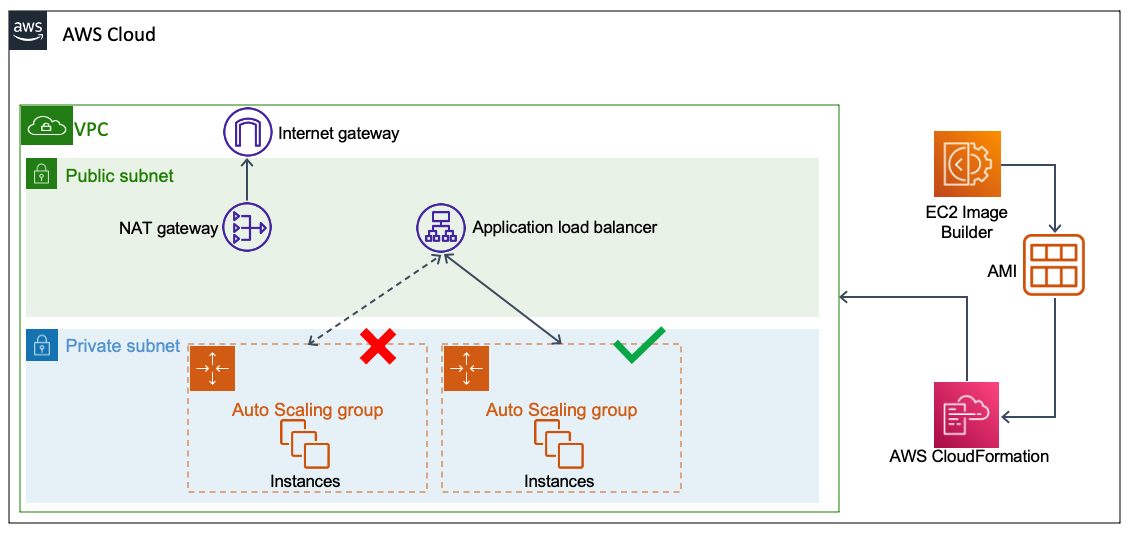



Deploy The Ami Builder Pipeline Aws Well Architected Labs




Using Nested Stacks With Aws Cdk Dev Community



Ssmセッションマネージャーでコンソールアクセスできるec2をcloudformationで自動作成する方法



Aws Cfn Ecs Ami Updates Ecs Cluster Auto Update Ami Cfn Yml At Master Intelligentpathways Aws Cfn Ecs Ami Updates Github




Lab 2 Datacenter Connectivity Networking Immersion Day




Vers Un Monde Sans Bastion Le Blog Amazon Web Services



Cloudformation 一撃で Ec2 の Blue Green Deployment の Codepipeline を構築する Developersio




Deploy Ghost On Aws Using Cloudformation Part 03




Shipping Aws Ec2 Logs To Cloudwatch With The Cloudwatch Agent Tom Gregory
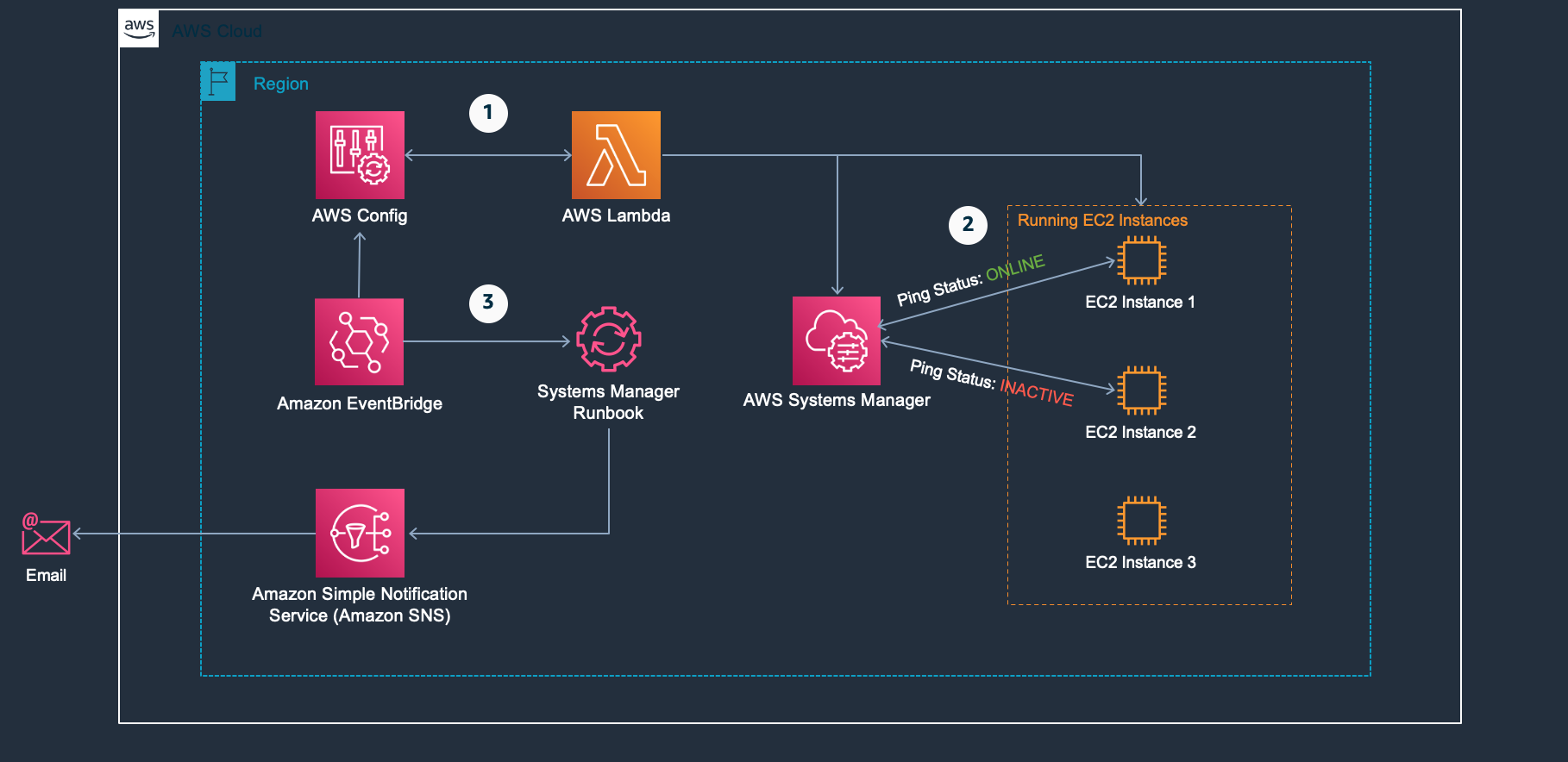



Improve Monitoring Of Aws Systems Manager Agent Cloudpro Exam Prep
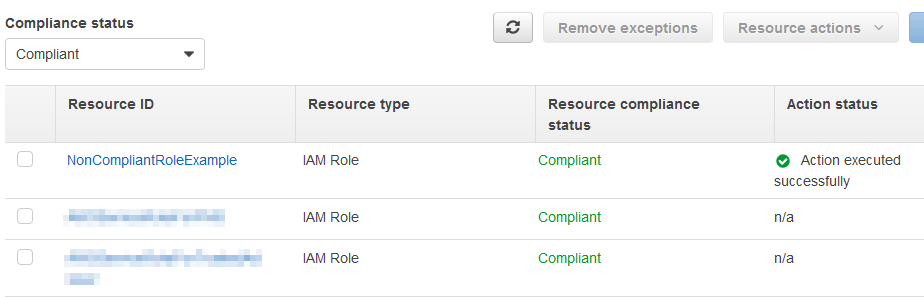



Applying Managed Instance Policy Best Practices Aws Management Governance Blog



Ec2 Volume Manager Demo Stateful Server Yaml At Master Binxio Ec2 Volume Manager Github




Sql Server Fciをfsx For Windowsを使って構築する Awsリソース編 Developersio
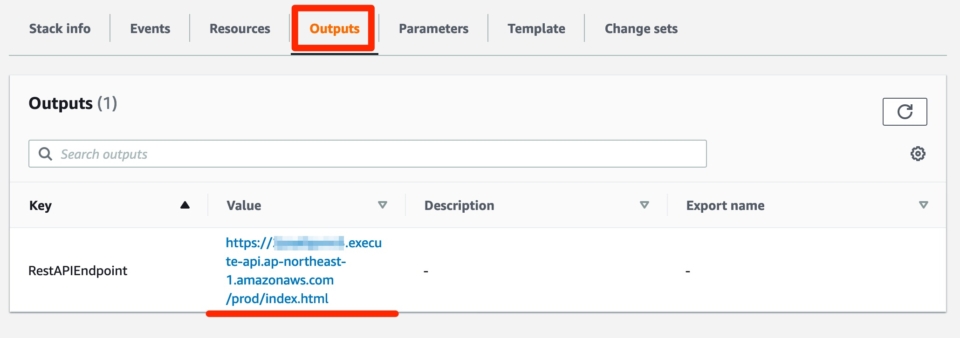



Cloudformationを使ってapi Gatewayとec2でrest Apiを構築してみる Developersio




Deploy Ghost On Aws Using Cloudformation Part 03




Aws Ecs White Paper Pdf Amazon Web Services Computer Data
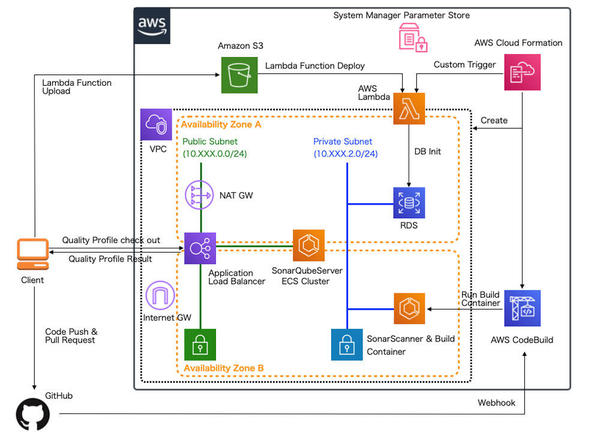



連載 Awsで実践 基盤構築 デプロイ自動化 40 継続的インテグレーション環境の構築 1 開発ソフトウェア It製品の事例 解説記事




News Noise Page 14




Steve Roberts Noise




Stackery Announces The Availability Of Bastion Modules On The Cloudformation Public Registry



Applying Managed Instance Policy Best Practices Aws Management Governance Blog




Create A Cluster And Run Ls Dyna Github




Integrating Aws Cloudformation With Aws Systems Manager Parameter Store Aws Management Governance Blog




Who Holds The Keys To The Kingdom Part 1 Of 2 Ermetic




Amazon Ec2 Noise Page 4



Introduction To Aws Systems Manager
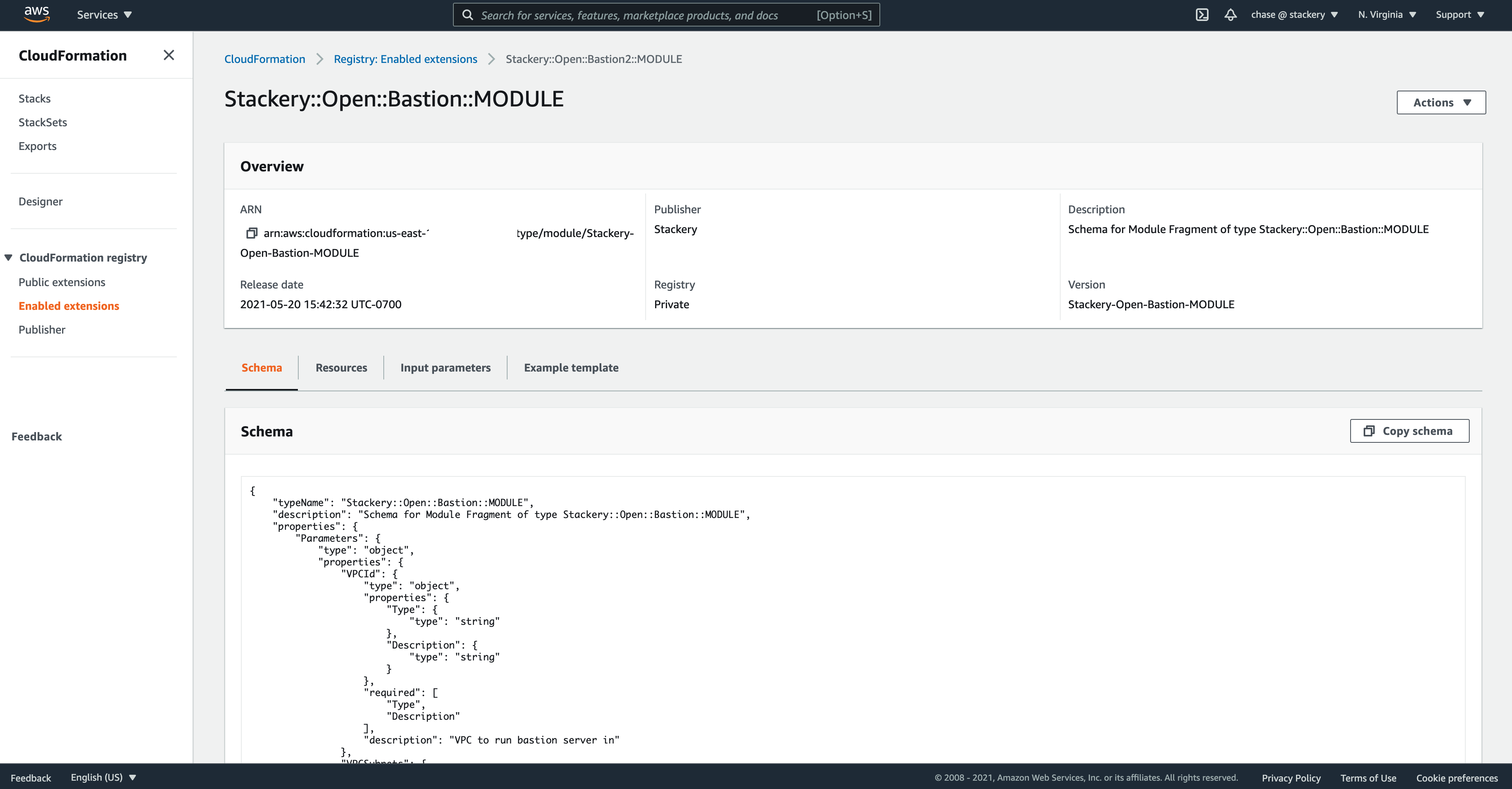



Stackery Announces The Availability Of Bastion Modules On The Cloudformation Public Registry
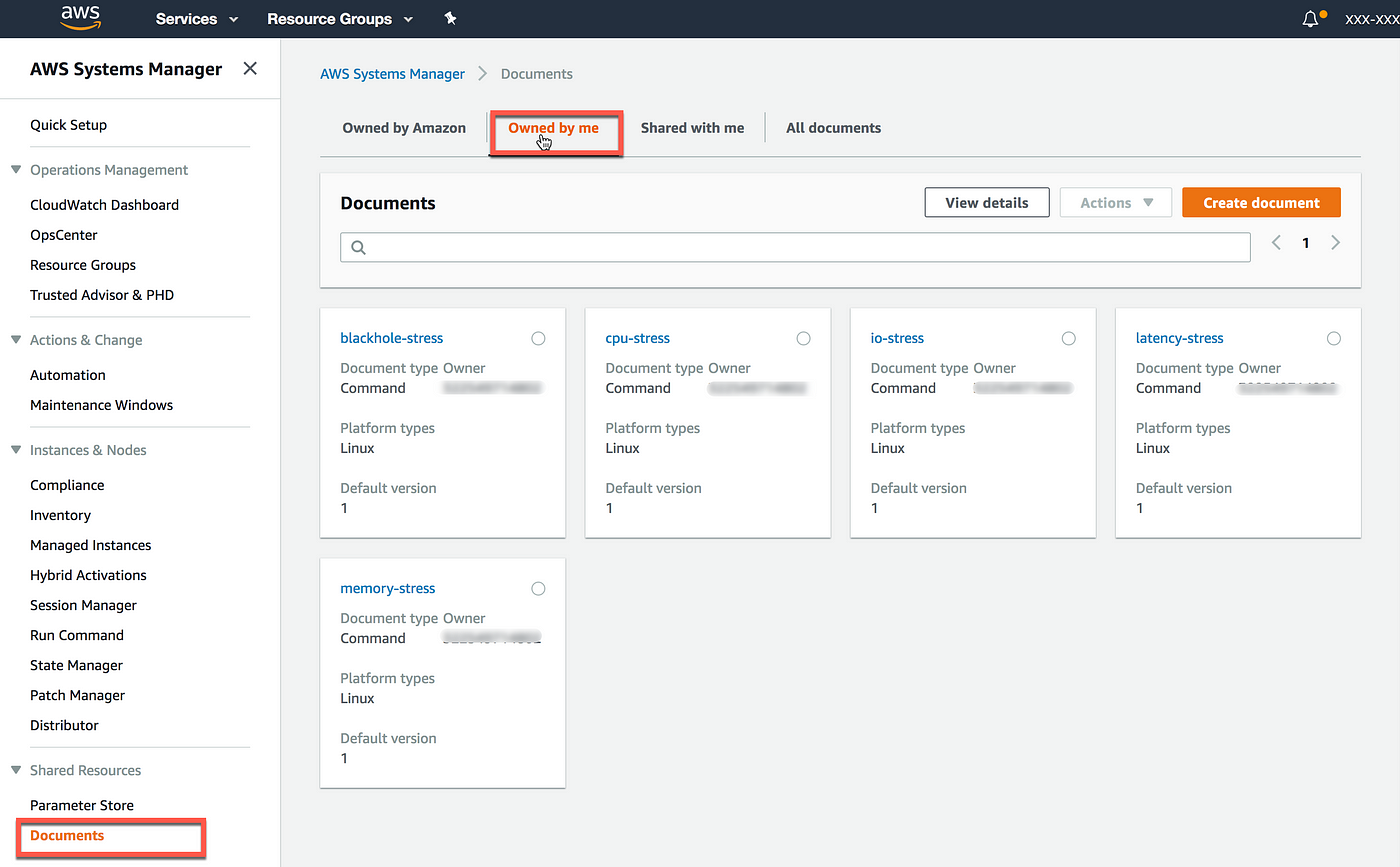



Injecting Chaos To Amazon Ec2 Using Aws System Manager



Threatmodeler Setup Quickstart S3 Amazonaws Com




Automated Configuration Of Session Manager Without An Internet Gateway Aws Management Governance Blog




How To Secure Your Instance Metadata Service On Aws Using Aws Systems Manager Run Commands Cevo



Cloudformation Gotchas And Lessons Learned By Osvaldas Rokas Medium
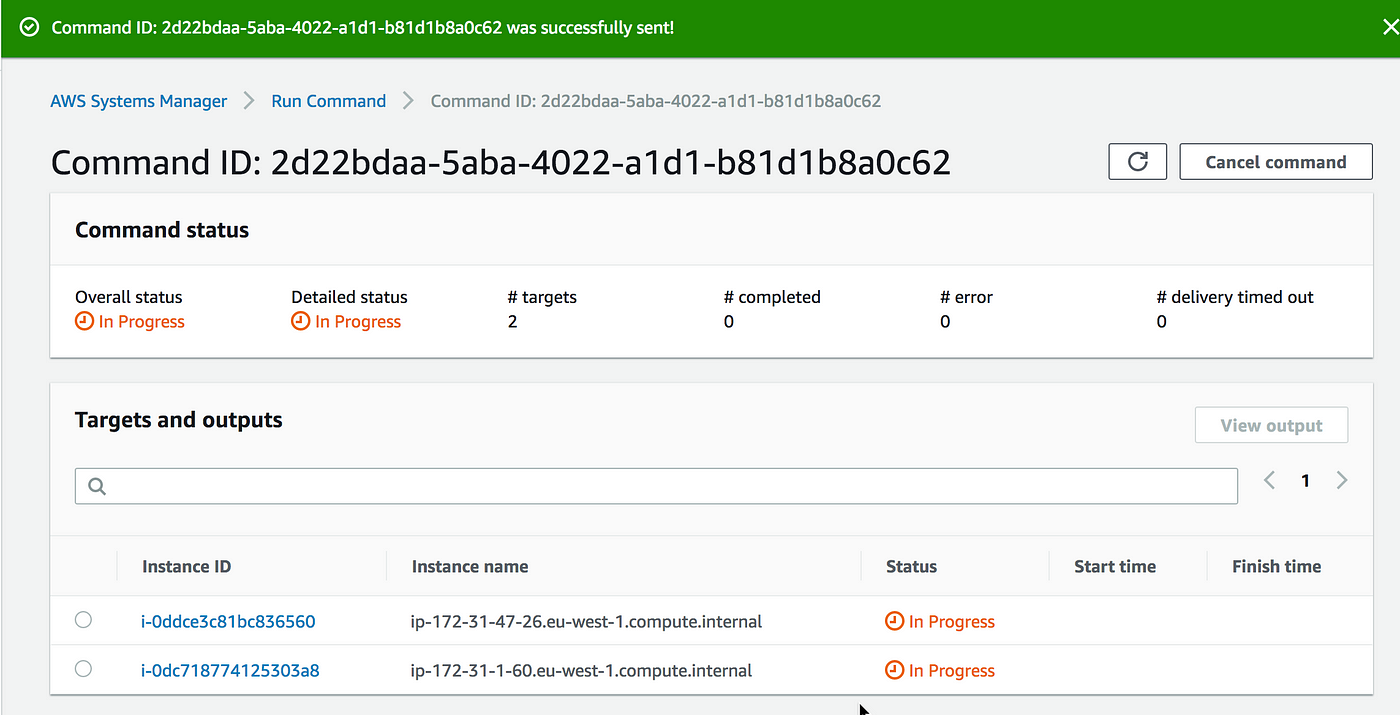



Chaos Engineering On Amazon Ec2 Using Aws System Manager Ssm The Cloud Architect



Aws Automation



Aws Automation
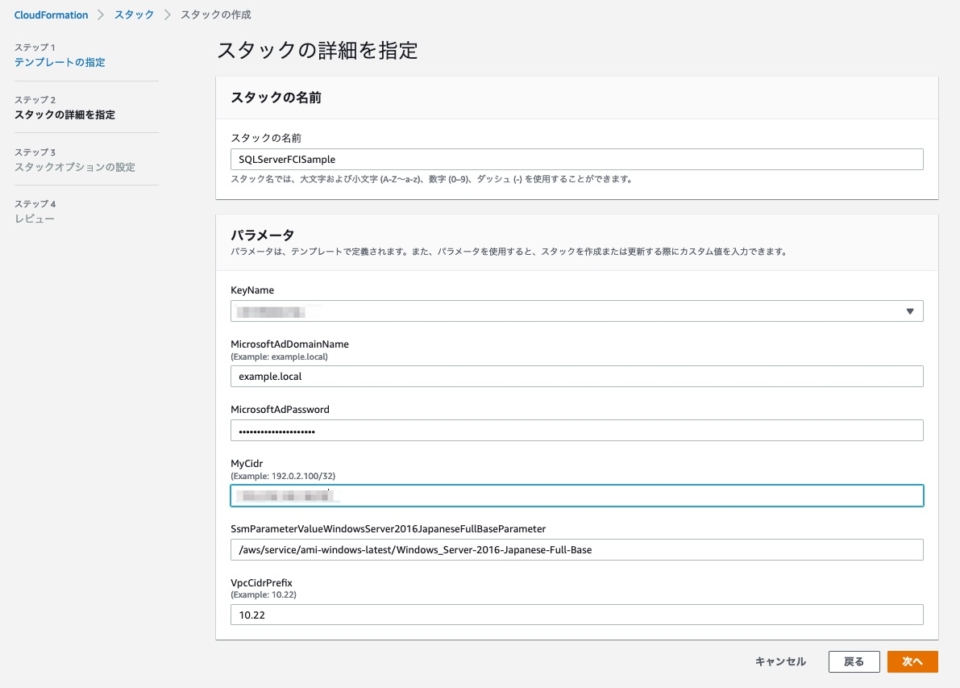



Sql Server Fciをfsx For Windowsを使って構築する Awsリソース編 Developersio




Shipping Aws Ec2 Logs To Cloudwatch With The Cloudwatch Agent Tom Gregory




Aws 실습 4주차 1 Cloudformation으로 환경배포




How To Install Aws Ssm Agent On Centos 8 Centos 7 Computingforgeeks




Setting Up Custom Aws Config Rule That Checks The Os Cis Compliance Aws Management Governance Blog



C 7yntgim8xihm



Taswar Bhatti The Synonyms Of Software Simplicity



Aws Cloudformation Evaluation Using The Proov Platform




Deploy Ghost On Aws Using Cloudformation Part 03




Automated Configuration Of Session Manager Without An Internet Gateway Aws Management Governance Blog



Aws Launch Wizard For Quick Sql Server Always On Deployments



Injecting Chaos To Amazon Ec2 Using Aws System Manager



How To Connect An Ec2 Instance Via Systems Manager By Mert Saygi Medium




How To Secure Your Instance Metadata Service On Aws Using Aws Systems Manager Run Commands Cevo



Sql Server Fciをfsx For Windowsを使って構築する Awsリソース編 Developersio




How To Install Aws Ssm Agent On Centos 8 Centos 7 Computingforgeeks



How To Achieve A Secure Connection To Ec2 Virtual Servers With Session Manager Without The Need Of Encryption Keys Financial Solutions




Part 4 Wordpress Ec2 Instance In Asg With Rds Database And Alb Awesome Aws Cdk Dev Community
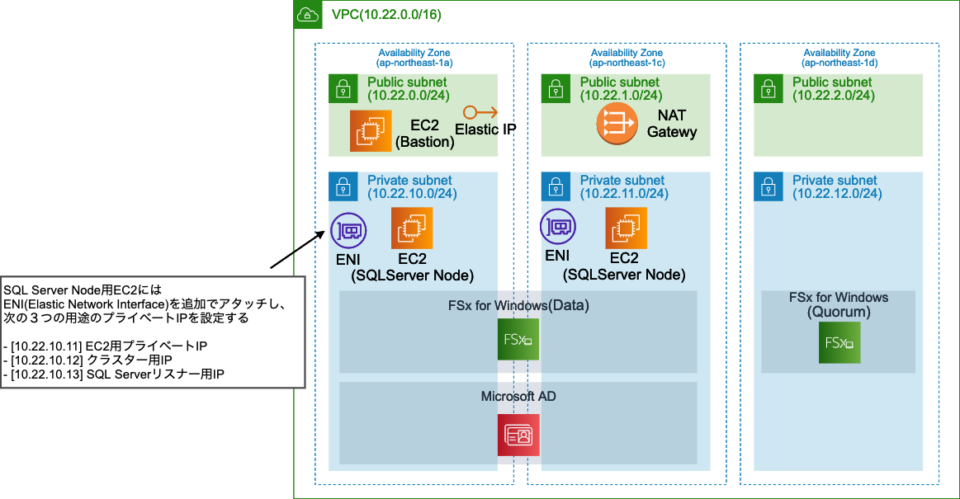



Sql Server Fciをfsx For Windowsを使って構築する Awsリソース編 Developersio
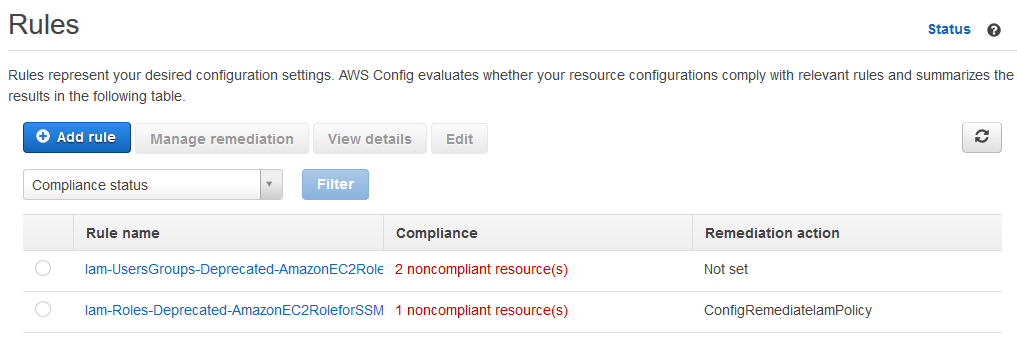



Applying Managed Instance Policy Best Practices Aws Management Governance Blog



1



0 件のコメント:
コメントを投稿